Future-Proof Your Business with Our Cyber Security Online Risk Assessment Tool
Get ahead of cyber security risks, and stay ahead, with the online risk assessment tool that does it all.
Get Ahead of Your Digital Risks
Identify cybersecurity risks quickly and effectively with our Cyber Security Online Risk Assessment Tool. Created for mid-level organisations, we've designed a tool that determines security vulnerabilities so you can protect your organisation from potential threats and ensure your information security objectives are aligned – and receive a comprehensive, actionable report on how to reduce your risks in the process.
Protect your organisation - try our Online Risk Assessment Tool today.
Get a Risk Assessment & Report

Safeguard Your Business
Cyber attacks continue evolving as technology does, meaning it's more important than ever to know your risks and their potential impact. A data breach or cyber attack can have an irreversible impact on your business and brand - it's imperative you have cybersecurity risk management in place to ensure you're protected.
It's also important to understand that cyber threats don't start and end with adversarial threats. They can include a whole range of potential risks, including natural disasters, system failures, and human error. All of these risks can result in data loss, destruction of information assets, and exposure of sensitive data.
Our Cyber Security Online Risk Assessment Tool allows you to:
- Identify threats and weaknesses in your information systems
- Understand which of your business assets require additional protection with a risk rating
- Assess your current security objectives and align cyber security policies with your business operations
- Develop procedures and improve your risk management framework to protect your organisation from vulnerabilities
A Cyber Risk Assessment Game Changer
While there are some online risk assessment tools out there, none are quite as quick and efficient as we liked - and no digital tool aligns with the Australian Government's Essential Eight. We wanted to create something that would make identifying and mitigating cyber risks as easy as possible. No long processes, no time-consuming site visits, no delayed reporting – just a simple, expert-informed, government-aligned risk assessment that provides you with actionable items to ensure you’re protected.
Our Cyber Security Risk Assessment Tool allows users to work through a series of questions to identify potential risks your cyber security teams need to be aware of so that you know how to put your best foot forward when it comes to protecting your business.
- Specially designed to align with the eight essential mitigation strategies outlined by the Australian Government
- Quick and extremely effective - we know you're busy, and this is the most efficient tool out there. No consultant visits necessary!
- Cost-effective - more insight at an even more affordable price
- Comprehensive reporting - receive a report that provides insight, outcomes, and an action plan for your identified risks


Get informed with our detailed risk assessment report
Knowledge is power, and we want to make sure your organisation is powerful in the face of cyber threats. Our Cyber Security Online Risk Assessment Tool provides you with a thorough report that details the gaps in your current security controls, gives clarity for decision-making and process-building, and outlines action items to ensure you're protected.
Use this report not only to develop internal security frameworks and drive management action, but also to provide insight for insurers, banks, shareholders, potential investors, and more. It’s your guaranteed pathway to cyber security and protection.
Our Online Risk Assessment Process
Our Cyber Security Online Risk Assessment Tool is simple and quick. Once you've signed up, you'll work through a series of questions based on the Australian Government's Essential Eight. Upon completion, you'll receive a thorough report on the identified risks and potential impact, and the appropriate action your organisation needs to take to ensure you're protected.
What’s included in my tailored risk assessment report?
We customise every risk assessment report for each individual business. Each report includes:
- An overview of the assessment, including scope and restrictions
- Positive findings
- Recommendations
- Immediate action items for the highest risks
- Short-term improvements
- Long-term improvements
We assess a range of security elements, including network security, backups, infrastructure and more. Get an idea of what will be included in your cyber security risk assessment report below.
VIEW SAMPLE REPORT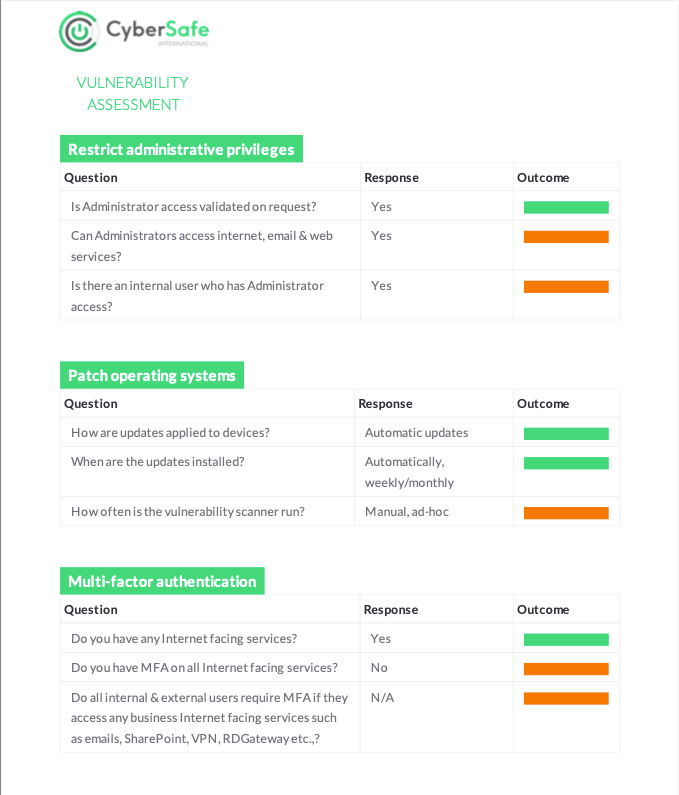

Why CyberSafe International?
Our group of companies have been in the cyber security business for a long time, and we're passionate about educating organisations and their teams on potential risks to ensure they're protected and will continue to thrive for years to come.
We offer a wide range of cybersecurity training and eLearning in short, bite-sized modules that will ensure your team is informed.
All of our products and training are created by experts in cybersecurity and online learning, and backed by the Australian Government Cyber Security Centre's Essential Eight.
With CyberSafe International, you're guaranteed the highest quality service, expert advice, and the most current information on the current cybersecurity climate.
GET STARTEDFrequently Asked Questions
What is a cyber security risk assessment?
A cyber security risk assessment identifies which of your information assets may be at threat of a cyber attack. By performing a thorough assessment of your organisation, it indicates potential risks you may be susceptible to, and gives you insight into how you can mitigate these identified threats, with an action plan to protect your business.
What are some potential cybersecurity threats that an online risk assessment can prepare me for?
There is an abundance of potential cybersecurity threats to your business, and these continue to increase as technology advances. However, there are a few more common threats to be aware of:
- Phishing: an attack where fake communications are sent out to trick somebody into following instructions within the email. For example, requesting payment information for an online account or masquerading as a supplier invoice.
- Malware: As the name suggests, malware is malicious - some malware is used to access sensitive information, others are designed for extortion, and others are used simply to cause disruption.
- Ransomware: your information system is essentially 'held hostage' until the victim has paid a ransom. A user will download malware, often specifically designed to target vulnerabilities in a system.
- Man-in-the-middle attack (MITM): attackers can intercept communications (e.g. emails) and take personal information.
These are only a handful of some of the most common cyber security attacks - there are many more you should be aware of. Luckily, our Cyber Security Risk Assessment Tool performs a risk assessment of your organisation, discovers the gaps in your protection, and gives you actionable advice on how to cover any potential vulnerabilities.
Who is Cybersafe's Cyber Security Online Risk Assessment Tool for?
We recommend our Cyber Security Online Risk Assessment Tool for mid-market businesses and organisations.
What is the Australian Government Essential Eight?
The Essential Eight is a set of mitigation strategies from the Australia Cyber Security Centre's (ACSC) Strategies to Mitigate Cyber Security Incidents, and was introduced as a baseline for cyber protection. It outlines essential strategies for businesses to have in place to protect against cyber threats and prevent a range of potential risks in your information systems.
The Essential Eight is regularly updated and is based on the ACSC's experience in cyber threat intelligence - so you know that this is the most relevant, up-to-date information on cyber security and protection in Australia.
What other CyberSafe products can help reduce my risk?
- Cybersafety Training - a range of short modules to educate your team and arm them with the information they need to be safe
- ICT Usage & Compliance - we provide IT and communications policy templates developed by IT professionals, so you know that you're covered
- Certified CyberSafe - a standard awarded to organisations where 80% of the team have achieved a CyberSafe Certificate of Proficiency and have proven compliance with the Australian Government's Essential Eight through CyberSafe's online assessment application